Get Latest Exploit Reports
The term 'vulnerability' is often mentioned in connection with computer security, in many different contexts.
In its broadest sense, the term 'vulnerability' is associated with some violation of a security policy. This may be due to weak security rules, or it may be that there is a problem within the software itself. In theory, all computer systems have vulnerabilities; whether or not they are serious depends on whether or not they are used to cause damage to the system.
Vulnerability
An information security "vulnerability" is a mistake in software that can be directly used by a hacker to gain access to a system or network.
CVE considers a mistake a vulnerability if it allows an attacker to use it to violate a reasonable security policy for that system (this excludes entirely "open" security policies in which all users are trusted, or where there is no consideration of risk to the system).
For CVE, a vulnerability is a state in a computing system (or set of systems) that either:
allows an attacker to execute commands as another user
allows an attacker to access data that is contrary to the specified access restrictions for that data
allows an attacker to pose as another entity
allows an attacker to conduct a denial of service
Examples of vulnerabilities include:
phf (remote command execution as user "nobody")
rpc.ttdbserverd (remote command execution as root)
world-writeable password file (modification of system-critical data)
default password (remote command execution or other access)
denial of service problems that allow an attacker to cause a Blue Screen of Death
smurf (denial of service by flooding a network)
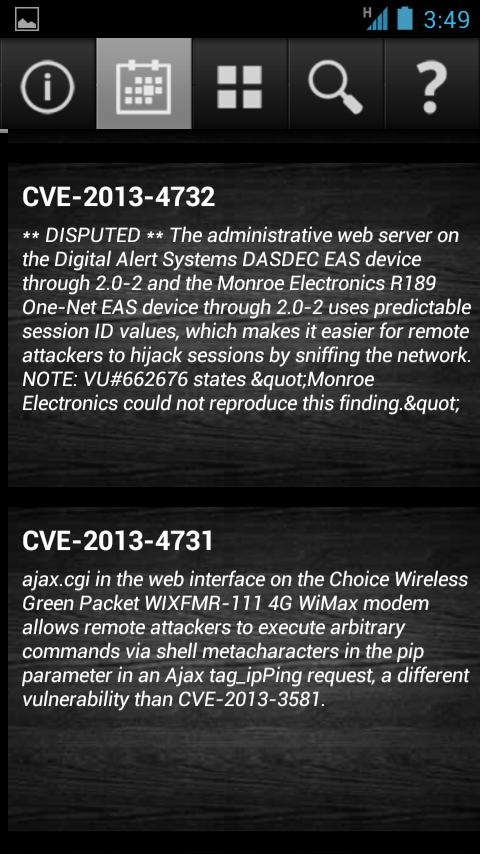
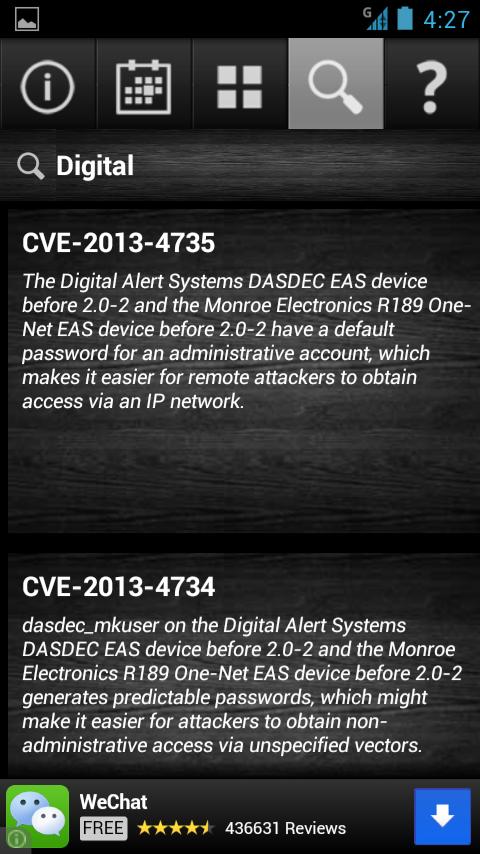
Our Application tries to put everything together So that as soon as a Vulnerability has been detected
you get notified,and If you have a website or working on such technology which are in the High Risk you can
fix it. Even if you are unable to fix the Issue let us know .
Our Team Can Help you FIX .